If you are doing an inspection of the other side’s computers, it is not as simple as pushing the “on” buttons of their computers. The various operations you wish to perform may raise operation-stopping objections, unless you have agreed on the protocol of the inspection beforehand.
We have a short, solid, checklist protocol. Use it as the basis of discussed agreement. Avoid on-site road-block arguments, before everyone spends time and money to get to the place for the on-site inspection of the electronically stored information.
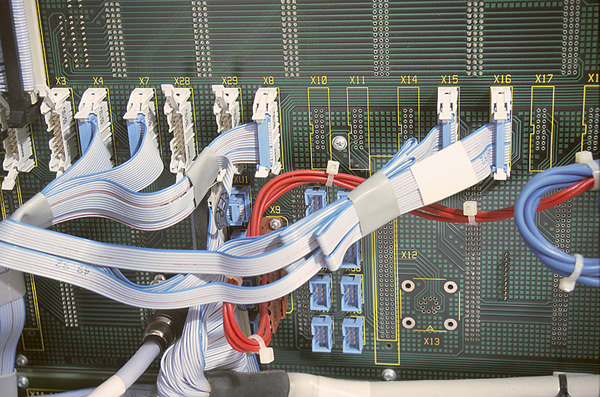
On-site inspections of Electronically Stored Information (ESI) become necessary when you want to insure that you have discovered the valuable evidence buried in the other side’s computers. Such an inspection may be the only way to insure that you have the metadata without destruction.
Ordinarily if you are inspecting computer or Electronic Storage Information (ESI) devices of your adversary, you will have an expert of your own advising you. Some experts will suggest items like we have in this Protocol Onsite Inspection. They are items that should be agreed upon by all the parties before the expert arrives on the scene. Other experts will assume that you have covered items such as we have in this Protocol Onsite Inspection. In any case you do not want to be caught short at the site, when your adversary attorney starts raising points and objections to going forward with the inspection.
Over 98% of most correspondence and data is stored electronically, not in file cabinets. Most external and internal correspondence is either e-mail or it is written on a computer, and the sender’s copy is kept electronically. It’s no wonder that you may want to get into the electronic storage of the adversary and see what resides there. This form gives you the advice of a mentor in the format of a legal form checklist for use in the discovery process with an adversary. It is one of our series of checklist and proven tips articles.
We are selling Protocol Onsite Inspection for only $11.